What is Digital Footprint?
A Digital Footprint or an electronic footprint is the data and information trail that is left behind due to a user’s online activity over the internet. Digital footprints are proof of your digital presence including all digital engagements, interactions, visits, etc. In short, it is the mark of your virtual presence.
Types of Digital Footprint
| Active Digital Footprint | Passive Digital Footprint |
|
|
Importance of Digital Footprints in Digital Identities
Digital Footprints are highly important in digital identities. Here is a brief overview of how DFs impact digital identities:
Positive Impact
- Digital Footprints are highly effective in the KYC Identity Verification process. The digital trails of user’s data and information are highly useful in creating authentic user profiles.
- Enhanced User Experience is another benefit of Digital Footprints as they enable targeted advertisements and personalized ad campaigns minimizing advertising bombardment.
- Positive Digital Footprints can help devise effective online marketing campaigns and improve personal branding.
- Digital Footprints can also help users maintain trust and authenticity in their digital identities where their positive DFs can support their legally compliant activities.
Negative Impact
- Digital Footprints are always at risk of being misused for Identity theft, Fraud, and other illicit activities.
- Excessive Digital Footprints can be tracked and breach the data privacy rights of users.
- Negative Digital Footprints can damage user’s reputations and can cause loss of opportunities.
- Digital Footprints can be used to make deepfakes through AI and misused for many crimes like ATO Fraud, etc.
Check out how you can Prevent Identity Theft with KYC.
What Activities Makeup a Digital Footprint?
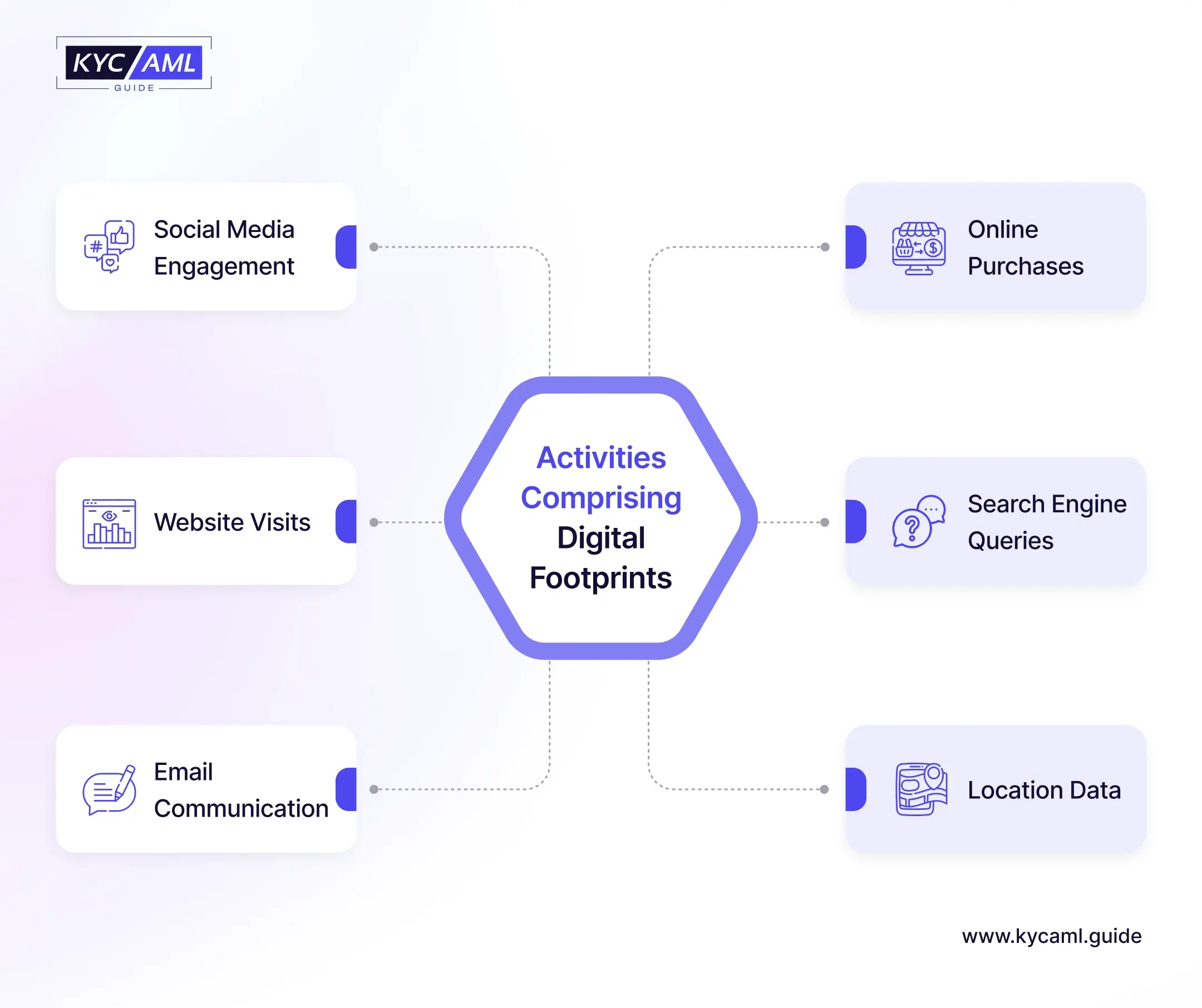
| Social Media Engagement |
|
| Online Purchases |
|
| Website Visits |
|
| Search Engine Queries |
|
| Email Communication |
|
| Location Data |
|
Also Read: Protecting Your Digital Footprint
The Role of Digital Footprints in KYC (Know Your Customer)
As mentioned earlier Digital Footprints play a key role in the KYC Identification process. Here are the main aspects in which these data trails can be used in enhancing KYC processes:
1) KYC Document Verification
The data and information in the form of digital footprints can be used by KYC Vendors to verify the KYC Documents and the user information present on them. For example, if a person has paid a utility bill online through the website, then this digital footprint can be used to verify and match the correct address, and payment details.
2) Enhanced Biometric Data
In Biometric KYC, the digital footprints can support facial, fingerprint, and voice recognition in biometrics. All social media activity and conversations can be used to enhance the datasets present in a biometric identification system.
3) Enhanced Social Media Verification
The Identity verification of social media users has been facing issues ever since. Genuine user’s user-identifiable information can be used to verify the customers and prevent hacking.
4) Single Sign-On (SSO)
Single Sign-On (SSO) also uses digital footprints including IP address, behavioral patterns, and device information to allow single credentials to be used for multiple sign-ups online. For example, Google Sign-In is an example of SSO using digital footprints of customers where their Gmail ID is used for authenticating multiple services like Facebook, LinkedIn, and even different freelance websites.
Also Read: Future of Digital Footprint Checkers
Risks of Using Digital Footprints in Digital Identities
The biggest risk that Digital Footprints pose to Digital Identities is the loss of control and the loss of the right to privacy of data. There’s much hype on Self-Sovereign Identity (SSI) that is focused on empowering users to have control over their own digital identities. But if the digital footprints are there, and easily accessible then users by definition have no control over their identities.
Secondly, the risk of identity theft, impersonation, and fraud is always there as long as digital footprints exist and people are not aware of the dangers of misuse of their data. Recent statistics revealed that only 9% of global internet users have asked a company to review their personal information retained in their customer records. The number is alarming because if users do not understand their right to privacy, then the debate of SSI or consent-based information sharing ends and the control is with someone else. However, this concept applies to third-party services and not government databases as governments lawfully collect and record personal information for identification and security purposes.
Final Thoughts
Digital Identities make the foundation of your digital persona and make the world see you as who you want to be. But protecting your identity is the first and most important thing to safeguard your sensitive information. For this purpose, use the trusted platforms, and follow the best practices while using the internet. Moreover, whenever you share some information online during sign-up or registration, use only relevant information and always ask and review the data privacy policy and your rights. Last but not least keep a close watch on your digital footprints to protect your information.