Identity Verification Vs Authentication: A Brief Comparison
Mostly, both Identity Verification and Identity Authentication are widely used terms in KYC and AML. Interchangeably, these terms are used to explain a single concept of digital identity management for security compliance. However, these terms have different concepts behind them. If we look into a deeper definition of both, we shall know the difference. Let’s define each of them.
Identity Verification
Identity Verification refers to the process of verifying the collected information about a customer’s actual and documented identity. Essentially, Identity Verification is the most fundamental concept in KYC and AML compliance as everything revolves around a customer’s Identity. For example, a bank requires an ID card, Proof of Address, and other details to open up a bank account.
Identity Authentication
As the name refers, Authentication means verifying the identity as they have posed it. Here, the verification procedure is more strict and cross-verifies the provided information with the claimed Identity. For example, a password or biometric authentication is required at an ATM machine to confirm that the transaction is carried out by you.
Importance Of Identity Verification and Identity Authentication
Seemingly, both processes complement each other in the KYC process. Initially, Identity Verification is carried out to collect information about the customer. Likewise, it established the digital identity recorded in a database. On the other hand, Identity Authentication brings scrutiny and filtered confirmation in the system. Ultimately, these two combine to form a secure digital identity system. In this way, a fraudster or scammer can be identified if he is trying to bypass any security measure. Especially, in the course of KYC and AML, Identity Verification vs Authentication is of high importance.
The following trend shows an increase in the revenue trends of Identity Verification methods from 2023-2027 in US Billion Dollars. The trend shows a sharp increase in revenue generated by Identity Verification service providers. In 2023 the revenue is recorded at US$ 10.16 billion as of June whereas it is predicted to rise at US$ 18.12 billion.
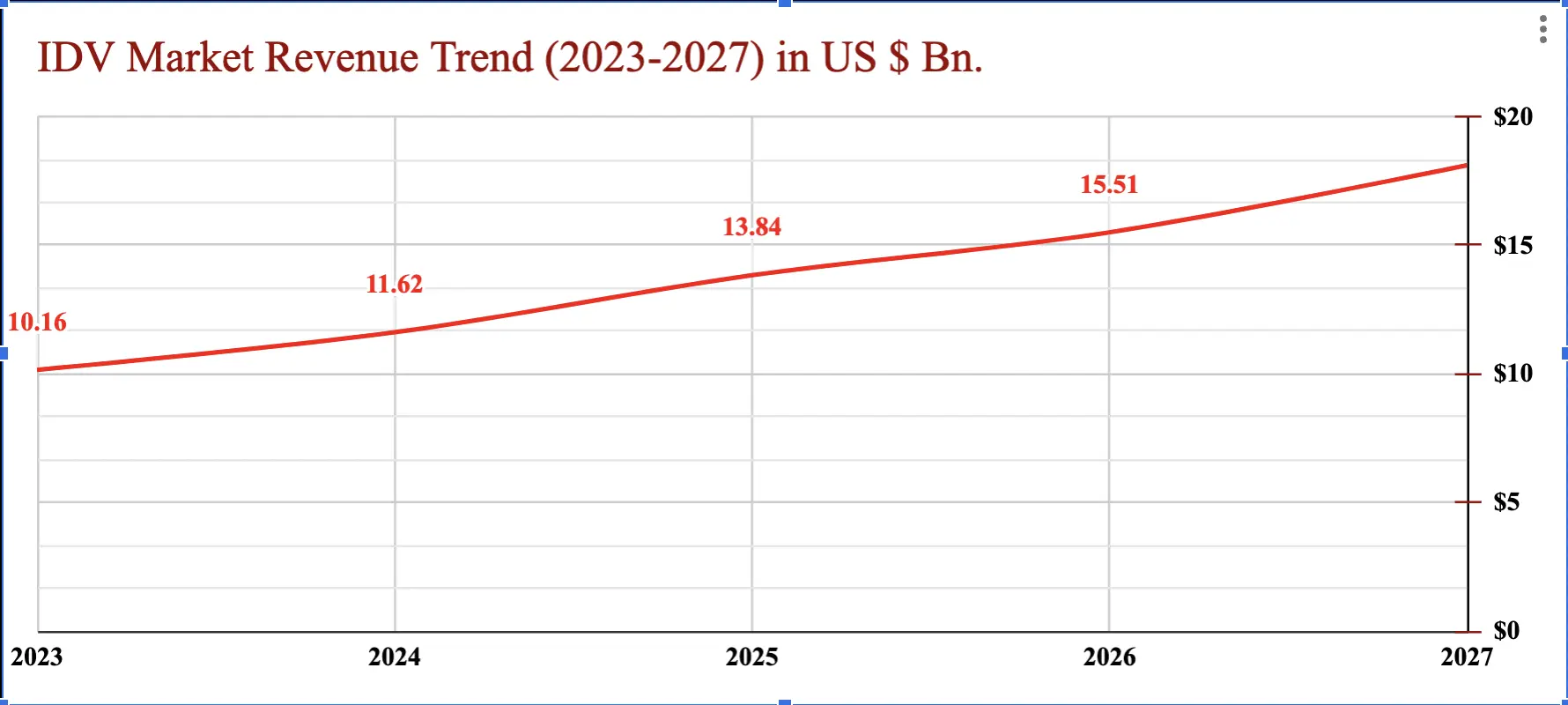
(Source: Statista)
Difference Between Identity, Verification & Authentication
Actually, Identification, Verification, and Authentication are three different steps. Following is the main difference between them:
| Identification | Verification | Authentication |
| Initial Stage of Digital Identity Management | Secondary Stage of Digital ID Management | Third and Final Stage of Digital ID Management |
| Initial data collection of the customer | Cross-verifying the collected data with database record | Allowing customers through a recurring verification process to use the service |
| Signing up process | Verifying the details by cross-matching the records | Signing in process |
Identity Verification is normally considered the combination of the first two. Similarly, Identity Authentication is the combination of Identification and Authentication. Overall, there’s a thin line difference between Identity Verification vs Authentication. However, the process still requires these three steps to completely ensure that only valid and authentic personnel are being allowed to utilize the services.
Identity Verification Vs Authentication: A Simple Scenario
Basically, it is the identity-proofing system that best explains the working of the process. Look a the example of the dialog below digital identity in each case:

Above, is a simple scenario of Identity Verification vs Authentication. Clearly, one can see the level of connectivity between the application and the user. It all depends on the trust that a customer builds in the system by being honest and law-abiding.
Latest Trends in ID Verification & Authentication
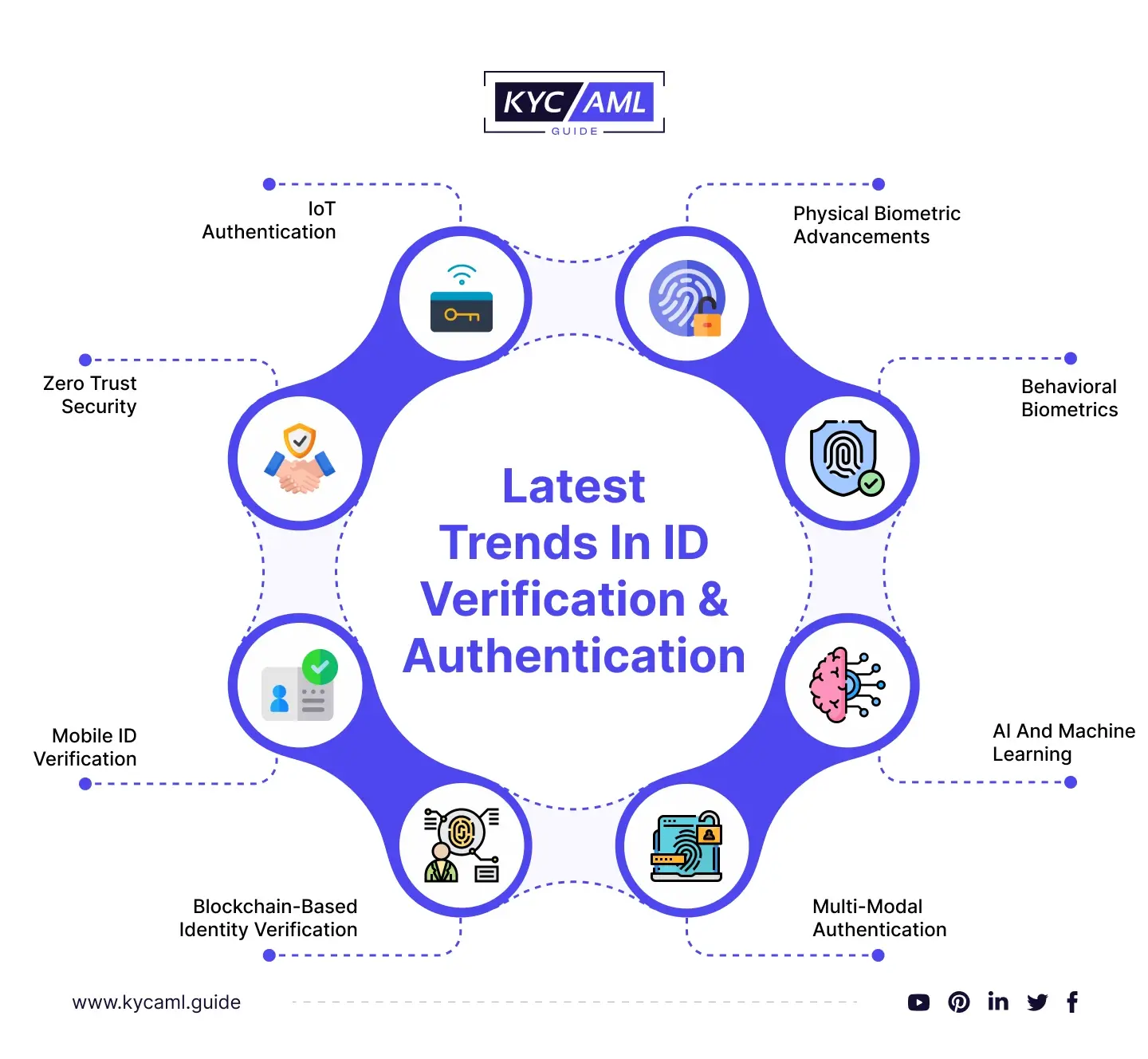
| 1 | Physical Biometric Advancements | Biometric authentication methods, such as facial recognition, voice recognition, and fingerprint scanning continue to evolve. These technologies are becoming more accurate and secure making them increasingly popular for identity verification. |
| 2 | Behavioral Biometrics | Beyond traditional biometrics, behavioral biometrics analyze patterns in user behavior, such as typing speed, mouse movements, and touch gestures, to authenticate users. |
| 3 | AI and Machine Learning | AI-powered authentication systems are improving fraud detection by analyzing user behavior and identifying anomalies. They can adapt to new threats and become more accurate over time. Supplemented by Machine Learning, AI is now being integrated with other identity verification & authentication methods for improved accuracy & security. |
| 4 | Multi-Modal Authentication | It Combines multiple authentication methods such as fingerprint and facial recognition to enhance security and convenience. It is a combination of different authentication methods which adds protective layers to the identity verification system. |
| 5 | Blockchain-Based Identity Verification | Blockchain technology is being used to create decentralized and secure identity verification systems, giving users more control over their personal data. By leveraging the decentralization factor and immutable nature of blockchain, identities can be securely stored and verified, reducing the risk of data breaches and identity fraud. |
| 6 | Mobile ID Verification | It enables mobile devices for identity verification, often through mobile apps or SMS-based verification codes. It is user-friendly but considered less secure due to being easily accessible by the general public. Service providers are working on improving the mechanism of Mobile ID verification. |
| 7 | Zero Trust Security | Moving away from the traditional perimeter-based security model, Zero Trust assumes that threats can come from both outside and inside an organization. Identity verification plays a crucial role in verifying trust at every access point. |
| 8 | IoT Authentication | With the proliferation of Internet of Things (IoT) devices, robust authentication methods for IoT are becoming increasingly important to protect data and user privacy. |
Wrap-Up
The difference between Identity Verification and Authentication is a crucial concept in digital identity management. Instead of favoring one over the other, it is imperative to recognize that both Identity Verification and Identity Authentication play equally important roles in establishing a robust and foolproof digital identity management system. A harmonic synergy between these two processes is key to ensuring the integrity and security of user identities.
Furthermore, it is essential for regulated entities to remain vigilant and stay abreast of the latest developments in KYC and AML guidelines. Compliance with evolving regulations is not just a best practice but a legal imperative to mitigate the risk of potential legal actions and maintain the trust of customers and stakeholders.